HackmeOut ! |
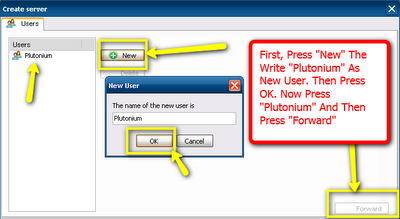
| CyberGate Tutorial and Free Download Posted: 23 Oct 2011 05:37 AM PDT In this article I'll be showing you how to install and setup a Hacking software called "Cybergate".This is a very effective Windows Hacking tool.These genre of Programs are commonly called "RATs (Remote Administration Tools)".It has almost all the features which a budding hacker needs to understand more about the programming and the vulnerabilities of the computer.With this tool you can virtually "CONTROL ANY WINDOWS COMPUTER ON THE PLANET!" .But you have to make sure you install a file called "server.exe" some how or the other.The details I'll be providing here. Features of CyberGate: Managers: File Manager Process Manager Service Manager Device Manager Window Manager Regitry Manager Installed Programs Active Port list Spy: Screen Capture Webcam Capture Password Recovery Keylogger Audio Capture Network Tools: Socks 4/5 Proxy HTTP Proxy Send File Download and Execute Open Webpage URL Redirection Extras: Dos Prompt Quick Search (for logs) Chat Extras (open-close CD-ROM etc.) And Alot More! Setting up and Installing Cybergate: First of all download the software from this link.Make sure you don't download them from any website as such as it might be infected with some virus.Please make sure you disable your Anti-Virus before doing this as it might be detected as well.Don,t Worry the Anti-Virus is just over precautionary and tons of users worldwide you this software.If no you can always good about it ! File Details: Download: Free Download Cybergate v1.07.5 RAT File Size: 2.28 MB File Extension: .rar (Compressed Archive) 1. Start off by going to No-IP.com And Register. If You Have An Account There Already, Then Just Log In. 2. Once You've Logged In, Press "Add Host" 3. Now It's Time To "Choose Your Host Name". Hostname: YourHostName.no-ip.biz Don't Care About The Rest, Once You've Choosen Your Host Name, Press "Create Host" In The Lower Right Bottom. The Host Is Now Finished! Lets Move On To The No-IP Client. 1. The No-IP Client You Downloaded In The Beginning, Extract It To Your Desktop & Install It. 2. Now When You've Installed It, Open It Up , Log In With Your No-ip Username , Password. 3. When You're Logged In Press "Select Hosts" And Then Check That Little Box With Your Hostname. Note: Always Have No-IP Open When You Have Cybergate Open! There! Your No-IP Host ! Setting Up Cybergate 1.07.5 1. Extract The Cybergate File You Downloaded In The Beginning To Your Desktop! Once Extracted, Open It,Wait 20 Seconds For The Agreement To Pass! 2. When It's Open, Press: Control Center,Start. 3. Press: Control Center , Options , Select Listening Ports 4. Once You've Pressed The "Select Listening Ports" This Window Should Appear: 5.Firstly, Write "100" In That Little Box And Press The Blue Arrow. Then It Should Appear Under "Active Ports" Active Ports: The Port You Will Forward Later! Connections: Limit: The Max Amount Of Victims You Can Have. Connection Password: The Connection Password. Use "123456" [V] Show Password: (Shows Password) Once This Is Done, Press "Save"! 6. Now We'll Go To The: Control Center , Build , Create Server. User: First, Press "New" And Name It To: "Plutonium". Once Done, Press "OK" Now Just Double Click On "Plutonium" Or Press "Plutonium" And Then Press "Forward" 7. Now We're In The "Connection" Tab. First, Press "127.0.0.1 - 999" And Then Press Delete.Now Press "Add" And Write Your Hostname In It + :100.Like This: YourHostName.No-ip.biz:100 Change The Identification To: Cyber Change The PW To: 123456 Note: If You Want To Try The Server On Yourself, Then Delete Both: - 127.0.0.1:999 - YourHostName.No-ip.biz And Replace Them With; 127.0.0.1:100 Since 127.0.0.1 Means "Local Computer or LAN Internet" Make The DNS/HostName Server First Though! DNS: Your Host Name, EG: Quote: YourHostName.no-ip.biz Port: The Port You Will Forward Later. Identification: The slave Name PW: The Password You Wrote In The Options, "123456" 8. Once You're Done With Theese, You'll Move On To The "Installation" Tab. 9. Have The Same Settings As I Do, And Follow The Instructions In The Image! Install Directory: Where The Server Installs, %System% %Windows% %Root% %Program Files% %Other% Use The "System"! Boot: This Is The "Startup" Option. Have Everything Checked.Press "Random" 5 Times And It Will Startup On Your slave Everytime They Start Their Computer! Directory: Where The Virus Folder Installs File Name: What The File Will Be Inside The Folder. Inject Into: What Process It Injects into, Use Default Browser! [V] Persistance: Keeps Trying To Inject Until Succed. [V] Hide File: Hides The File, (Not FUD Though!) [V] CCD: Changes The Creation Date From 16th July To 4 September 2005. Mutex: Mutex Of The Server, Just Press Random A Couple Of Times! There We Go, You've Now Completed The "Installation" Tab! Skip The Message of Keylogger Since They Are Pre-Set Already! 10. You Should Now Have Trumbled Into The "Antis" Tab, Have Everything Checked! (Except SANDBOXIE If You Are Gonna TRY IT ON YOURSELF!) Ok, The Final Tab.. "Creation Of The Server". Have Every Setting As Me! [V] Use Icon: Yes [V] Delayed Execution: (How Many Seconds It Takes Until Your Server Injects And They Pop Up In Your RAT) [V] Google Chrome PW: Yes, Steals Their GC Passwords :) [X] Bind Files: No, Get An Real Binder Instead! (Have Your Server Crypted Though First!) [X] Compress With UPX: Makes The Server Smaller But More AV's Detects It! So after doing all that you have successfully setup your own RAT server which is ready to be tested on yours friends ! Troubleshooting: Make Sure That.... 1.You are properly port-forwarded if using a router. 2.You have the No-IP Client installed and running. 3.Your DNS entries are correctly spelled when building your server. 4.The password in Listening Ports and the password your server uses are identical. 5.You are Listening on the correct ports. 6.Your Firewall is letting connections through on the port you're listening on. 7.Your server is added to excluded files in your Antivirus and Firewall. What next ? Now all you have to do is send this file to your friend and make sure he opens it.Once he does so he just won't realize that you actually infected him and your getting all the data from his computer.Make sure you use it only to prank and not to misuse this tool in any way ! Credits: Plutonium |
| You are subscribed to email updates from Hackmeout! To stop receiving these emails, you may unsubscribe now. | Email delivery powered by Google |
| Google Inc., 20 West Kinzie, Chicago IL USA 60610 | |












No comments:
Post a Comment